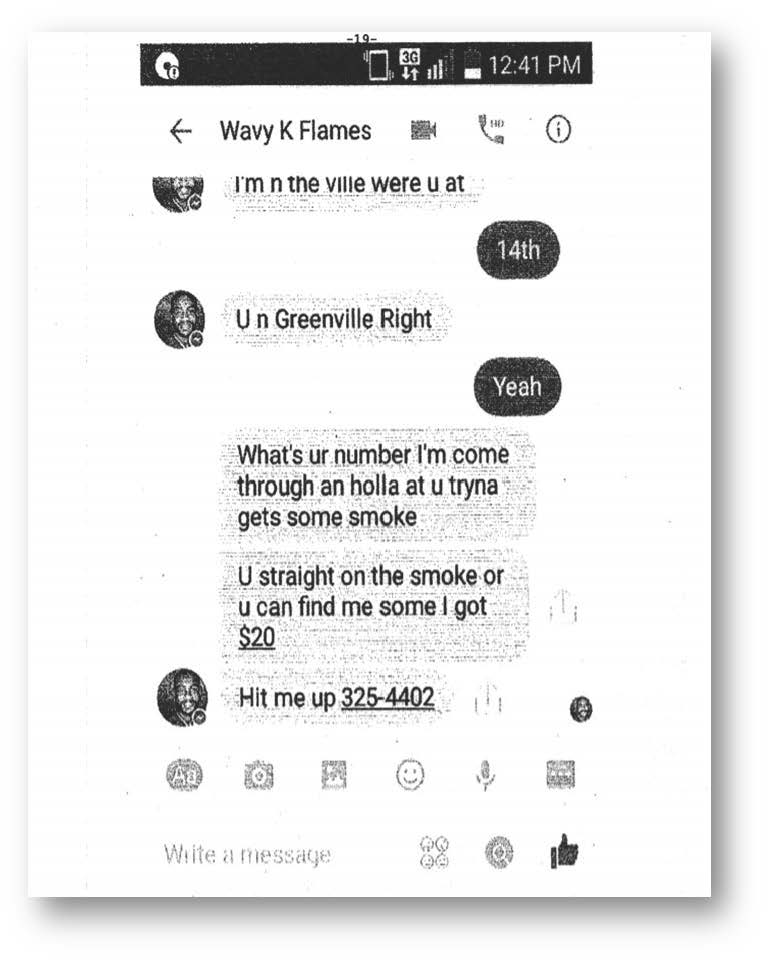
A common evidence question that arises is how to properly authenticate digital communications. We have written on the topic in several blogs: How Can a Party Show Authorship of a Social Media Post or Other Electronic Communication?, Authenticating Photographs Obtained from Social Media Platforms, Business Records: Posts, Chats, and Texts, New Guidance on Authenticating Social Media, Admissibility of Electronic Writings: Emails, Text Messages, and Social Networking Posts, and more.
Last year, I created a chart to highlight the ingredients of authentication our appellate courts found to be adequate or inadequate as a foundation for surveillance video (also see the accompanying blog, Surveillance Video- When It Comes In and When It Doesn’t). I’ve received positive feedback on the chart and practitioners have asked for more evidence content in this format. For a second installment, I chose digital communications.
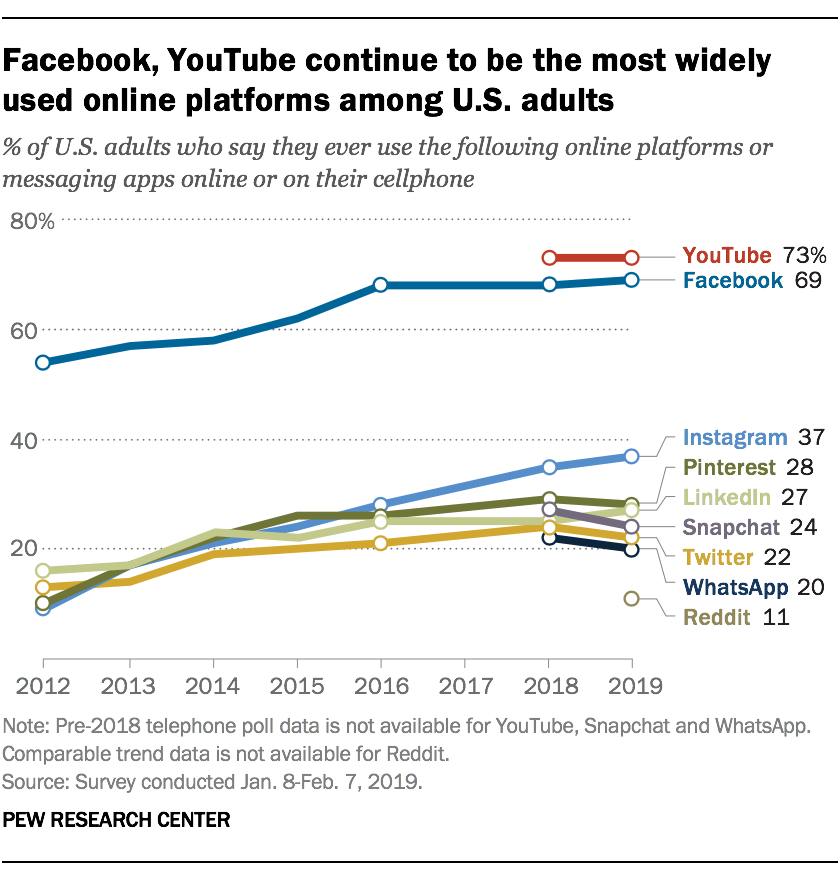 Nearly half of the 7.7 billion people in the world are on social media, and each of those users has an average of 8 different accounts. The rate is even higher in the U.S., with around 70% of the population active on social media for an average of 2 hours every day. You can find more jaw-dropping statistics
Nearly half of the 7.7 billion people in the world are on social media, and each of those users has an average of 8 different accounts. The rate is even higher in the U.S., with around 70% of the population active on social media for an average of 2 hours every day. You can find more jaw-dropping statistics