Earlier this year, the Fourth Circuit decided United States v. Zelaya-Veliz, 94 F.4th 321 (4th Cir. 2024). Phil summarized it here when it came out, but we thought it merited its own post because of its extended discussion of how the Fourth Amendment applies to search warrants for social media account information. The court’s discussion of the need for temporal limitations in such warrants is especially noteworthy, as is the court’s analysis of the scope of the information seized pursuant to the warrants approved by the court. We’ll start with a recap of the case, and then end with some thoughts for law enforcement and prosecutors, and for defenders.
New Guidance on Authenticating Social Media
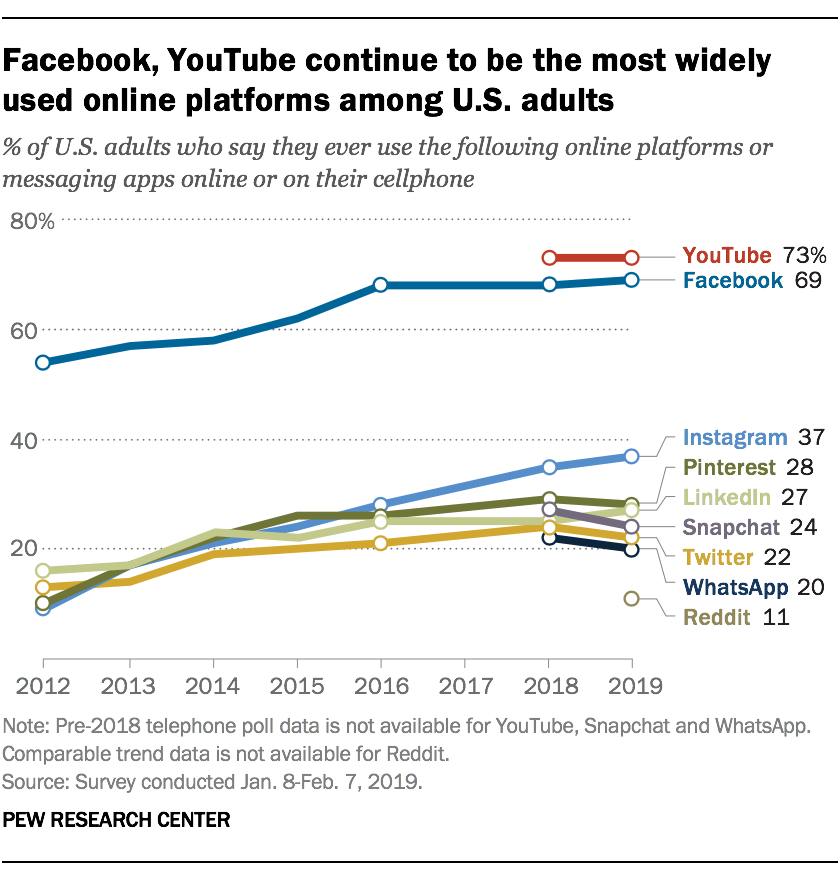 Nearly half of the 7.7 billion people in the world are on social media, and each of those users has an average of 8 different accounts. The rate is even higher in the U.S., with around 70% of the population active on social media for an average of 2 hours every day. You can find more jaw-dropping statistics here.
Nearly half of the 7.7 billion people in the world are on social media, and each of those users has an average of 8 different accounts. The rate is even higher in the U.S., with around 70% of the population active on social media for an average of 2 hours every day. You can find more jaw-dropping statistics here.
Given these trends, it’s no surprise that social media evidence is showing up more frequently in criminal cases. A quick search for criminal cases mentioning the most common social media platforms brought up well over 100 North Carolina cases decided in the last decade, but only a few of those cases have directly analyzed the authentication requirements for this type of evidence. The Court of Appeals recent decision in State v. Clemons, __ N.C. App. __ (Dec. 1, 2020) provides some additional guidance in this important area.
State v. Thompson Tells a Tale of Two Facebook Screenshots
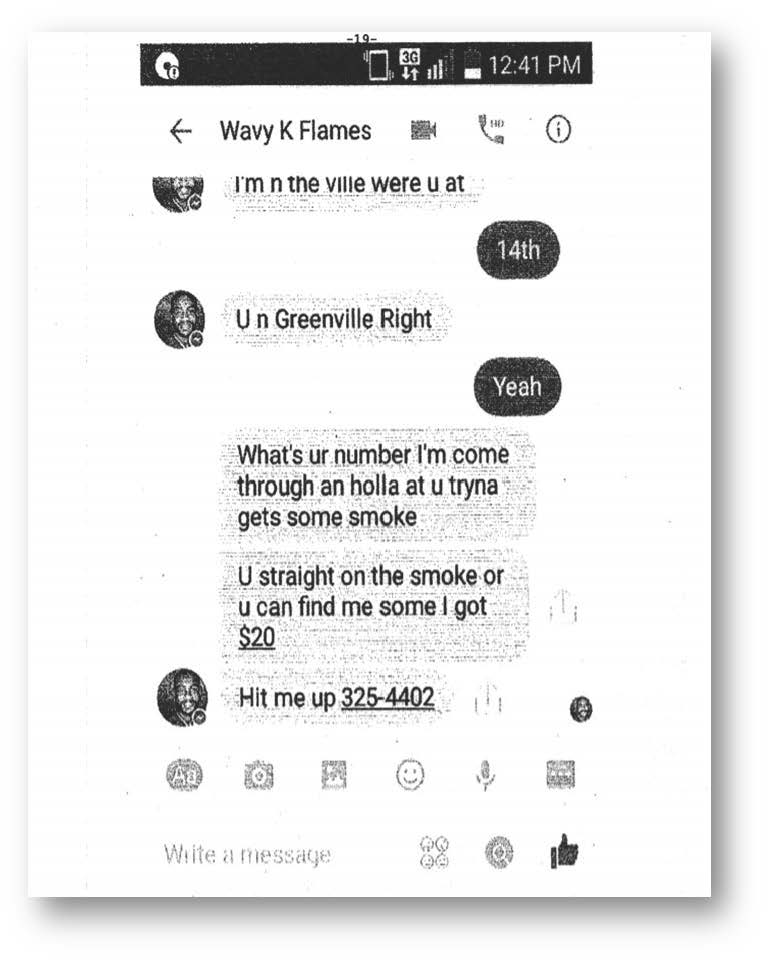 After Roshawn Thompson picked up his cousin Kendall Rascoe from the Greenville mall in November 2014, Thompson and a friend, Andre Grey, robbed Rascoe at gunpoint. At Thompson’s armed robbery trial, his defense attorney sought to cross examine Rascoe about Facebook messages he sent to Thompson earlier in the day asking whether Thompson could get some marijuana for him while he was in Greenville. Rascoe denied sending the message and testified that he just happened to run into Thompson at the mall. The State objected to the admission of the screenshot of the messages.
After Roshawn Thompson picked up his cousin Kendall Rascoe from the Greenville mall in November 2014, Thompson and a friend, Andre Grey, robbed Rascoe at gunpoint. At Thompson’s armed robbery trial, his defense attorney sought to cross examine Rascoe about Facebook messages he sent to Thompson earlier in the day asking whether Thompson could get some marijuana for him while he was in Greenville. Rascoe denied sending the message and testified that he just happened to run into Thompson at the mall. The State objected to the admission of the screenshot of the messages.
Later in the trial, the State sought to introduce a screenshot of a picture of Thompson and Grey copied from Thompson’s Facebook page. Rascoe showed the investigating detective the picture for purposes of identifying Thompson and Grey. Thompson objected to the admission of the screenshot, in which both of his middle fingers were extended.
How did the trial court rule? Did it make the right call?
May an Officer Assume a False Identity Online in Order to “Friend” a Suspect?
Officers are allowed to misrepresent their identities in the course of their investigations: they may pose as drug buyers, or prostitutes, or members of an organized crime syndicate. Is the same thing true online? In other words, may an officer claim to be someone else in order to “friend” a suspect on social media and thereby gain access to whatever information the suspect has posted? The answer isn’t clear yet, but I would guess that courts ultimately will say yes.
Legal Ethics and Social Media
The number of lawyers using Facebook, Twitter, LinkedIn and other social media networks grows daily. So too does the number of lawyers doing foolish and unethical things on those networks.
In this post I highlight some of the more egregious social media missteps made by lawyers in recent years, in the hope that other lawyers won’t repeat them. Then I describe how the Rules of Professional Conduct apply to social media both generally and in specific contexts such as investigations, litigation, and client testimonials.
The State Bar Addresses Lawyers, Judges, and Social Media
The North Carolina State Bar recently adopted 2014 FEO 8, an ethics opinion concerning lawyers’ and judges’ use of social media. The opinion answers some questions, but raises others.
Authenticating Photographs Taken from Social Media Sites
Suppose that the defendant is charged with a gang-related murder. The State seeks to establish that the defendant is a gang member by introducing a photograph that a detective found on the defendant’s Facebook page. The photograph shows the defendant flashing gang signs. The defendant argues that the picture can’t be authenticated, because digital photographs … Read more
Social Networking Prohibition for Sex Offenders Facially Unconstitutional
North Carolina’s ban on accessing commercial social networking sites by sex offenders is unconstitutional on its face, the court of appeals held this morning in State v. Packingham. Under G.S. 14-202.5, it is (was?) a Class I felony for any registered sex offender to access a commercial social networking web site where the offender knows … Read more
Cyberstalking
Furious that her ex-boyfriend slept with her best friend, defendant puts up a post on Facebook falsely stating that boyfriend enjoys intimate relations with inbred dogs (actually, the phrase “enjoys intimate relations” and the term “dogs” are mine; defendant herself employed far more colorful language). Since boyfriend and defendant are “friends” on Facebook, defendant knows … Read more