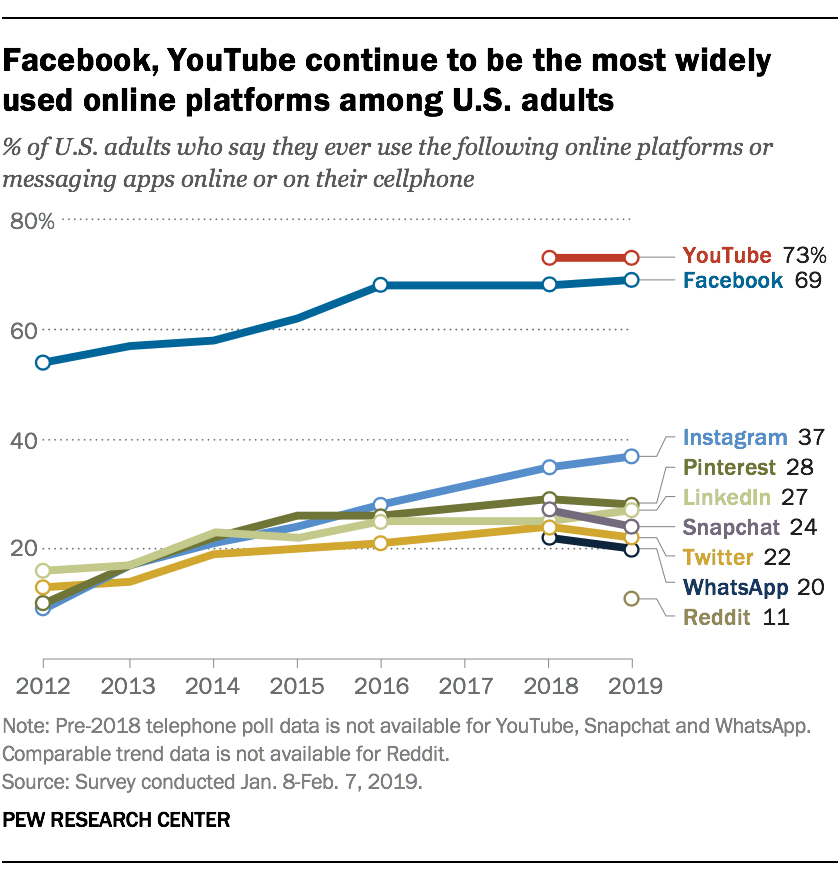
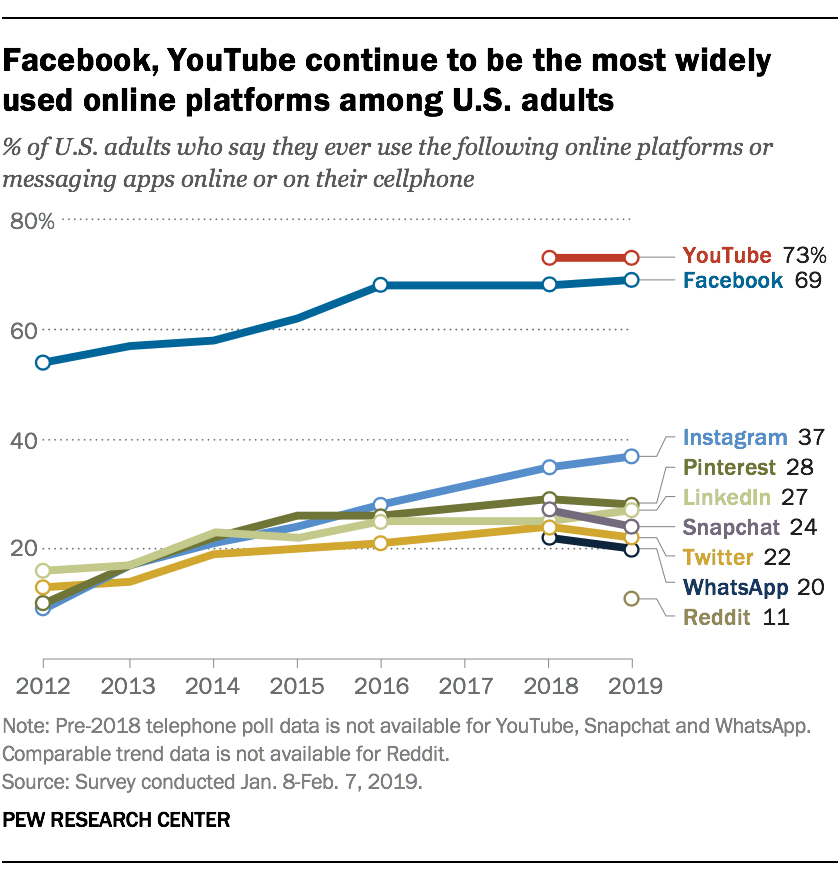
 Nearly half of the 7.7 billion people in the world are on social media, and each of those users has an average of 8 different accounts. The rate is even higher in the U.S., with around 70% of the population active on social media for an average of 2 hours every day. You can find more jaw-dropping statistics here.
Nearly half of the 7.7 billion people in the world are on social media, and each of those users has an average of 8 different accounts. The rate is even higher in the U.S., with around 70% of the population active on social media for an average of 2 hours every day. You can find more jaw-dropping statistics here.
Given these trends, it’s no surprise that social media evidence is showing up more frequently in criminal cases. A quick search for criminal cases mentioning the most common social media platforms brought up well over 100 North Carolina cases decided in the last decade, but only a few of those cases have directly analyzed the authentication requirements for this type of evidence. The Court of Appeals recent decision in State v. Clemons, __ N.C. App. __ (Dec. 1, 2020) provides some additional guidance in this important area.
Background and Evidence
Chris Tyner outlined the facts of this case in last week’s case summary, and the parties’ appellate briefs (available here and here) provide some additional background and context regarding the difficult history between the victim and the defendant. Just prior to the events at issue in this case, the defendant was in prison for another incident related to the victim and due to be released soon. The victim renewed a domestic violence protective order (DVPO) barring him from having any contact with her upon his release.
After the defendant was released, the victim began receiving calls and voicemails from the defendant on a blocked number, and she also received messages through their daughter’s Facebook account that she believed were posted by the defendant. After presenting the Facebook posts and other evidence to the police, the defendant was arrested and the communications ceased. At trial, the state introduced screenshots of the posts into evidence over the defendant’s objection. The trial court held that the evidence was sufficiently authenticated by the victim’s testimony. The defendant was convicted of violating the DVPO, and appealed.
Prior Guidance on Authenticating Social Media
The screenshot evidence in Clemons may remind you of State v. Ford, 245 N.C. App. 510 (2016), another social media case from a few years ago. In Ford, the state offered screenshots of the defendant’s Myspace page that contained incriminating images, titles, and captions, and the defendant argued that the evidence was not sufficiently authenticated. As Jeff Welty explained in his blog post about that case, the defendant in Ford argued that the state should have been required to offer some sort of technical foundation linking the defendant to the social media page, like account records from Myspace or IP address logs. The court disagreed, noting that authentication of evidence is a low bar requiring only prima facie evidence that the item is what it purports to be. Under that low standard, the court held that the Myspace screenshots were sufficiently authenticated under Rule 901(b)(4) based on the “distinctive characteristics” of the evidence itself, when taken in conjunction with the facts and circumstances of the case, such as the fact that the page was registered in the defendant’s nickname and it contained images of the defendant and his dog.
Jeff’s post closed by predicting that Ford “certainly won’t be the final word on the authentication of social media evidence” and readers should “stay tuned for further developments.” Clemons appears to be the next word in this area, and as predicted it contains several interesting developments:
(i) treating screenshots of social media as photographs;
(ii) applying Rule 901(b)(4) authentication principles to posts made through someone else’s social media account; and
(iii) shedding additional light on how much is “enough” when it comes to authenticating social media based on its distinctive characteristics.
Authentication Debate in Clemons
On appeal, the parties in Clemons offered very different interpretations of the authentication requirements for the social media screenshots. Under the state’s view, the screenshots were essentially photographs taken by the victim, capturing what she saw on her monitor. Therefore, they were properly authenticated by her trial testimony the she was the one who took the photographs, and the photographs fairly and accurately reflected what she saw. Deciding whether the contents of those photos implicated the defendant, and if so how much weight to give them, was a matter for the jury to decide: “After the screenshots were admitted into evidence, it was up to the jury to decide whether Defendant made this post based on the surrounding circumstances.” State’s Brief at 11, 12.
The defendant disagreed. In order to be relevant, the screenshots had to be viewed instead as written statements allegedly made by the defendant, and therefore they had to be authenticated as his statements before they could be admitted. The defendant pointed to past cases in which written statements were authenticated under Rule 901(b)(4) based on their “distinctive characteristics,” and argued that the state had failed to reach that threshold in this case. In the defendant’s view, the evidence before the trial judge may have indicated that the comments were not posted by the victim’s daughter, but “did not suggest in any way that the comments had been posted by [the defendant].” Defendant’s Brief at 13.
Which is It: Photos or Statements?
The Court of Appeals concluded that the screenshots in this case had to be authenticated as both photos and statements:
Before screenshots of an online written statement on social media can be admitted into evidence they must be authenticated as both a photograph and a written statement. To authenticate evidence in this manner, there must be circumstantial or direct evidence sufficient to conclude a screenshot accurately represents the content on the website it is claimed to come from and to conclude the written statement was made by who is claimed to have written it.
Clemons, slip op. at 1.
Authenticating the Photos:
Turning first to the photo authentication prong, the court held that the screenshots were authenticated by the victim’s testimony that “she took the screenshots of the comments on her Facebook posts, which showed the screenshots were in fact what they purported to be.” Id. at 19. Providing the same level of authentication for screenshots in future cases should be fairly easy to accomplish, but it brings up two points.
First, it’s worth remembering that the court is talking here about authenticating photos of social media comments, not authenticating photos taken from a social media account (e.g., a photo pulled from Instagram purportedly showing the defendant in possession of drugs). Authenticating that type of photograph may still require a different approach to foundation, as discussed in this blog post, although it is noteworthy that the screenshots in Ford did include photographs and videos and the court allowed the entire exhibit to be authenticated under Rule 901(b)(4).
Second, rather than characterizing a screenshot as a “photograph,” perhaps it could be viewed instead as a “duplicate” made by “electronic re-recording…or by other equivalent techniques which accurately reproduce the original” under Rule 1001(4)? That would seem to put it on more equal footing with other common methods of presenting digital evidence in court that qualify as originals, like an ordinary paper printout. See G.S. 8C-1, Rule 1001(4) (“If data are stored in a computer or similar device, any printout or other output readable by sight, shown to reflect the data accurately, is an ‘original'”). Either way, offering sufficient testimony from a witness to establish that the evidence is what it purports to be (i.e., an accurate representation of the original posts) should be a simple and straightforward task.
Authenticating the Statements:
Turning to the question of establishing authorship, the Clemons court applied Rule 901(b)(4) and held that “the Facebook comments were properly authenticated prior to admission as the distinctive characteristics of the post in conjunction with the circumstances are sufficient to conclude Defendant wrote the comments.” Clemons at 20. The court based its ruling on two key factors: access and circumstantial evidence. The defendant had access to the account because he was picked up from prison by the daughter who owned the account, and the daughter had a good relationship with the defendant as opposed to her “rocky” relationship with the victim, along with the fact that the messages began arriving shortly after the defendant was released. Moreover, other circumstantial evidence in the case generally supported the conclusion that “the person who posted these comments from the daughter’s Facebook account was Defendant.” Id. at 21. Evidence cited by the court included the defendant’s history of repeated DVPO violations against the victim, the fact that the messages were totally unlike the daughter’s normal communication with the victim, and the numerous phone calls and voicemails that the defendant made to the victim during the same time period as the social media posts. As noted above, this strikes me as an interesting extension of Ford, for a couple reasons.
First, unlike Ford, these statements were made on a social media account that unquestionably belonged to a different person, yet the individual messages could still be successfully authenticated as coming from the defendant, based on their distinctive characteristics and the circumstances of the case. That could be a significant detail in future cases dealing with posts or messages from blocked phone numbers, anonymous accounts, hacked profiles, etc.
Second, it’s clear that Rule 901(b)(4) allows a party to authenticate evidence based on its “distinctive characteristics, taken in conjunction with circumstances,” but when it comes to social media and other digital evidence, prior cases like Ford seemed to focus more on the distinctive characteristics of the evidence itself (account name, signature line, unique content of the messages, etc.). By contrast, Clemons seems to be focusing a little more broadly on the surrounding circumstances of the case (access to the account, similar conduct in the past, nature of the relationship, etc.). I’m not suggesting that either approach is wrong — on the contrary, I think both cases demonstrate that the rule means what it says, and the characteristics of the evidence have to be viewed “in conjunction with” the facts and circumstances of the case. So again, in future cases that may involve anonymous messages or unverified accounts, Clemons is a good reminder to think beyond the four corners of the screen.
In all likelihood, we still don’t have the final word on authenticating social media evidence, but Clemons is an interesting addition to a sparse yet important body of case law. Until next year, thanks for reading and please have a safe and healthy holiday.
